by Source Defense
Content Security Policy (CSP) and Subresource Integrity (SRI) were introduced with the right intentions: to limit unauthorized resource loading and to ensure that scripts cannot be tampered with undetected. In theory, CSP and SRI should provide strong protections against client-side threats like eSkimming. In practice, however, they fall short and often dramatically so.
The modern web simply evolved faster than these standards were designed to handle. The dynamic, script-heavy, API-driven architectures of today’s websites are fundamentally incompatible with rigid policy-based controls.
The Intent Behind CSP and SRI
CSP aims to restrict which domains can load scripts, images, stylesheets, and other resources. It allows security teams to define which sources are trusted, blocking everything else. SRI goes further by ensuring that externally loaded scripts match a known cryptographic hash. If the script is modified, the browser rejects it.
Both technologies were promising when websites were static and third-party scripts were limited in scope.
But that world no longer exists.
Why CSP Struggles in the Real World
CSP’s biggest challenge is the complexity of modern websites:
- Websites load dozens of third-party tags
- Those tags load additional scripts dynamically
- Many scripts require inline execution
- A wide range of legitimate domains must be allowed
- APIs and services change frequently
A strict CSP breaks site functionality. A lenient CSP allows malicious content through.
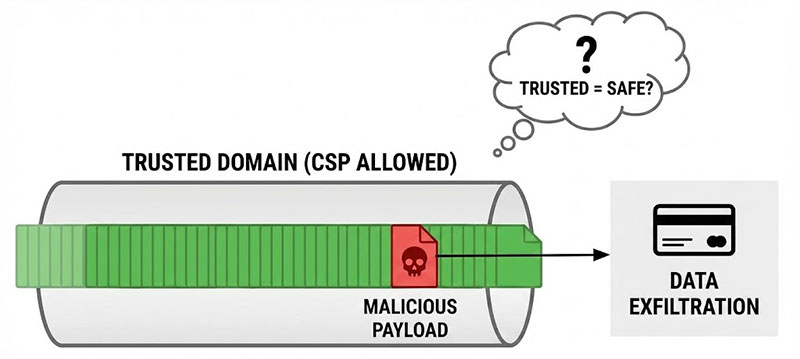
Most enterprises end up with CSP configurations that are permissive enough to nullify any meaningful security value. The biggest problem? CSP cannot prevent malicious behavior from a trusted domain.
If a third-party vendor is compromised, or a script updates automatically with new functionality, CSP offers zero protection.
SRI’s Fatal Limitation: Scripts Change Constantly
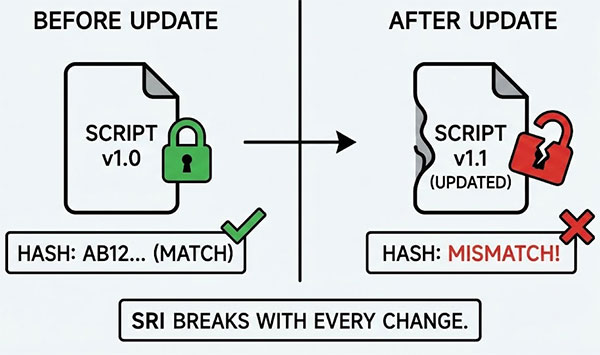
Subresource Integrity sounds ideal: enforce a hash so scripts cannot be modified. But SRI breaks immediately in real-world conditions:
- Third-party scripts update frequently
- Vendors cannot provide stable, predictable hashes
- A single update breaks the site if hashes aren’t updated instantly
- SRI cannot support dynamic content or A/B testing frameworks
Because external scripts change outside the organization’s control, SRI is simply not feasible at scale.
Attackers Routinely Bypass CSP/SRI
Sophisticated eSkimming campaigns abuse the weaknesses in these technologies every day.
Examples include:
- Compromising trusted third-party vendors (CSP can’t stop it)
- Injecting malicious code into scripts after SRI checks
- Hijacking legitimate domains that appear on allowlists
- Exploiting inline execution exceptions
- Using polyglot payloads that bypass overly broad rules
Attackers now target supply chain partners precisely because CSP/SRI cannot defend against them.
The Dynamic Web Renders Static Policies Obsolete
CSP and SRI are static controls in a dynamic environment.
They assume:
- Scripts do not change often
- Vendors do not chain-load unknown scripts
- Runtime behavior is consistent
- The organization controls all loaded resources
None of these assumptions reflect the reality of today’s web architectures.
The Better Approach: Behavioral Controls
To defend against modern eSkimming, organizations must look beyond source-level restrictions and hash controls. The solution is to monitor what scripts do, not where they come from.
Behavior-based controls focus on:
- Detecting unauthorized data access
- Blocking form interceptions
- Preventing DOM manipulation
- Stopping unauthorized network calls
- Enforcing least-privilege script policies
- Isolating untrusted scripts from sensitive user interactions
Instead of assuming a script is safe because of its origin or integrity at load time, behavioral systems continuously evaluate the script’s actions.
CSP and SRI Still Have Value—But Not for Skimming Prevention
CSP remains useful for reducing broad exposure to untrusted content. SRI helps protect against certain types of CDN tampering. But neither technology was built to stop client-side data theft, supply-chain compromise, or full-site eSkimming attacks.
The threat landscape has changed. The defensive tools must change with it.
