THE “PERFECT” MAGECART ATTACK: FAKE STRIPE FORM WITH ZERO EXTERNAL FOOTPRINT
August 26, 2025
The Source Defense Research Team has observed a rare and highly sophisticated Magecart attack that leaves almost no external trace. A hacker gained access to the merchant’s server and injected a first-party inline JavaScript designed to seamlessly replace the legitimate Stripe payment form with a convincing fake.
This attack is particularly dangerous because all stolen payment data is sent back to the merchant’s own server, where the attacker already has access – eliminating the need for any third-party exfiltration domains or suspicious outbound traffic.
How the attack works
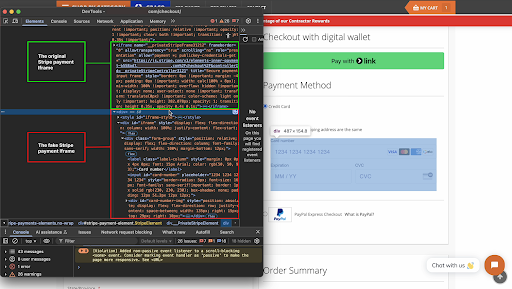
In the image below, you can see the deception in action:
- Original Stripe Payment Iframe (hidden) – The legitimate form remains in the page’s code but is visually hidden from the user.
- Fake Stripe Payment Iframe (displayed) – A pixel-perfect replica is injected and shown to the customer.
The attacker’s JavaScript collects the card data entered into the fake form and posts it back to the compromised merchant server, where it can be harvested undetected
Why this attack is so stealthy
- No 3rd-Party Domains – All communication is internal to the merchant’s infrastructure.
- No Suspicious Network Traffic – No requests to unknown domains that could raise red flags in monitoring tools.
- Server-Level Persistence – Since the attacker controls the merchant’s server, they can modify or restore the malicious script at will.
How does Source Defense protects you from such attacks?
In this case, there are no suspicious third-party scripts or outbound requests to detect — the attack is coming from a compromised first-party script on the merchant’s own server. This is exactly the type of scenario that traditional controls like CSP (Content Security Policy) would completely miss.
CSP only checks whether data is being sent to allowed or blocked domains, so as long as the script is communicating internally with the merchant’s own server, CSP will happily allow it. It has no ability to analyze what the script is doing or what data it’s touching.
Source Defense’s zero-trust, behavior-based approach operates differently. Our system continuously monitors all scripts on the page — regardless of their origin — and applies strict PCI data handling logic. The legitimate Stripe iframe is the only element expected to handle cardholder data; any other script attempting to interact with this information immediately triggers an alert.
When this malicious first-party script attempts to access cardholder information, Source Defense would:
- Detect the Unauthorized Behavior
The attempt to access PCI data is instantly recognized as abnormal activity based on predefined behavior profiles. - Classify and Prioritize the Incident
The event is marked as a security issue, with full context including the script responsible, the behaviors observed, and the affected pages. - Notify the Customer in Real Time
Alerts are delivered through multiple channels, ensuring security teams can take immediate action on their side.
How will you be alerted?
If such malicious activity were detected on a Source Defense-protected site, the following alerts would be generated:
- New Behaviors Identified:
- Accessing PCI data (by an unauthorized script)
- Attempting to read or transmit sensitive payment details
- Accessing PCI data (by an unauthorized script)
These alerts would be prominently displayed in:
- The Bell Notification Center
- The Dashboard Summary — marked in red for immediate visibility
- Script Behaviors Widget — showing the unauthorized PCI access attempt, highlighted in red
In addition, the user would also receive:
- An email notification detailing the newly detected behavior
- A webhook call to their SIEM, so their security team can immediately investigate and respond
Even though this attack involves no external domains and might bypass traditional monitoring tools like CSP or domain-based filters, our system proactively identifies the malicious action in real time — regardless of the script’s source.
To summarize: Even in this “perfect” Magecart scenario with no external footprint, Source Defense alerts you in real time — enabling a rapid response before the attack can impact your customers.
