PIXEL-PERFECT PAYPAL ATTACK QUIETLY GENERATED TO EVADE DETECTION
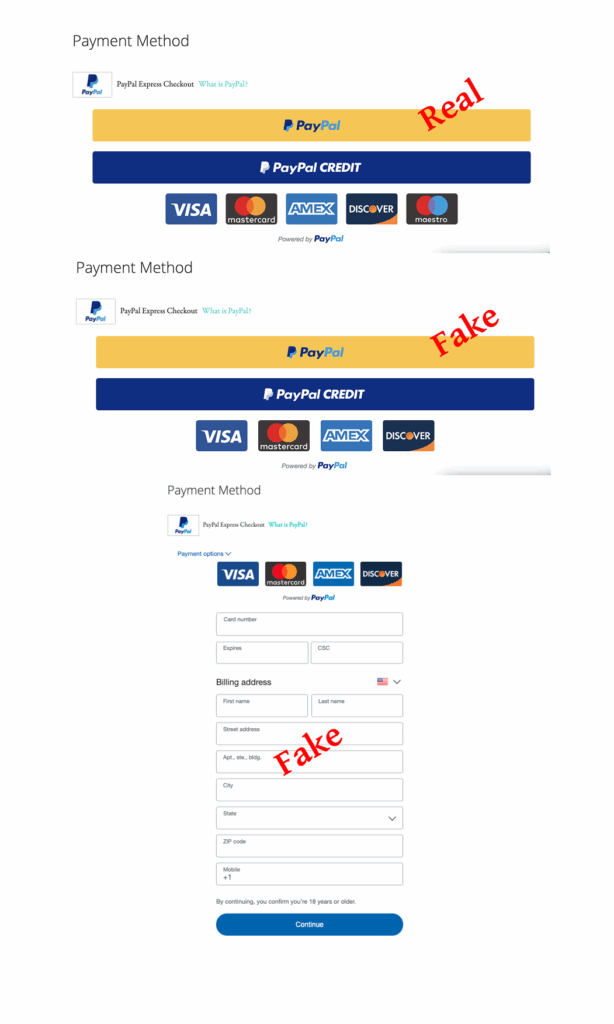
The Source Defense Research Team regularly uncovers Magecart-style attacks, but this latest discovery stands out for its deceptive precision. Attackers have replicated a PayPal payment form with near-perfect accuracy—omitting only the Maestro option—making it incredibly difficult to detect. The malicious code is injected via a compromised Google Tag Manager (GTM) and leverages advanced stealth tactics to silently capture and exfiltrate sensitive payment data, all while evading traditional security defenses.
Attack details
The breach begins with a compromised Google Tag Manager container that loads a malicious script from the domain foxicpeak[.]com – a domain that, until now, had largely evaded industry blacklists. When loaded onto the checkout page, this script injects an iframe using the srcdoc attribute to embed a complete, fake PayPal checkout form directly into the HTML. By rendering the interface inline, without calling external visual elements, the attack avoids traditional detection methods and maintains a high level of stealth.
This attack falls under the Double Entry category of Magecart attacks. Silent Skimming attacks typically rely on scripts that merely listen to form field inputs, but they cannot be implemented when external payment service providers (PSPs) handle checkout on their own domains. Double Entry attacks, by contrast, replicate the entire visual experience of the payment form and are becoming increasingly adept at doing so. This often involves loading additional assets such as images and CSS, making the attack heavier and more detectable. However, in this case, the attacker cleverly avoids external resource calls by embedding all design elements—including Base64-encoded images and inline styles—directly within the srcdoc. This drastically reduces network traffic, allowing the attack to remain inconspicuous while still delivering a near-perfect visual clone of PayPal’s checkout.
The fake iframe is positioned directly over the legitimate PayPal button using a high z-index value – a CSS property that controls the stacking order of elements on the page. This ensures the malicious iframe visually dominates, intercepting user clicks and form submissions, while the real PayPal iframe remains present underneath but inaccessible. Once the user interacts with the fake form, their sensitive data is exfiltrated to getlnfo[.]com—a deceptive lookalike domain crafted to resemble “getInfo.com” by substituting a lowercase “L” for an uppercase “I”. Unlike the less commonly observed domain that delivered the initial script, this one has been used in previous Magecart campaigns and is already recognized on several threat intelligence blacklists.
How Source Defense protects you
Source Defense would automatically prevent the GTM container from loading the malicious script from foxicpeak[.]com by blocking this domain at runtime. Even if the GTM tag is successfully injected, our policy engine either blocks or isolates third-party scripts and enforces strict execution controls, preventing them from manipulating the DOM or injecting iframes. This would stop the attack before the fake overlay could ever appear.
How you’d be alerted
In a live scenario, you’d receive alerts for:
- New script loaded from a blacklisted domain
- Attempts to access or collect PCI data
- Attempts to access or collect PII data
- Attempts to transfer data to a blacklisted domain
These alerts would be flagged in the dashboard, bell notification center, and the ‘Script behaviors’ and ‘Found in blacklist’ widgets—highlighted in red for immediate visibility.
Summary
This attack showcases how Magecart techniques continue to evolve, combining stealth with sophistication. Here’s what makes it particularly dangerous:
- Fake form embedded directly in-page: Avoids external loads to reduce detection while maintaining visual consistency.
- Triggered by a first-party script: Emphasizes the need to monitor even trusted, first-party code for malicious behavior.
- Loaded via Google Tag Manager (GTM): Bypasses whitelist-based defenses like Content Security Policy (CSP).
- Covers the real payment form from an external provider: Demonstrates that using a third-party PSP does not guarantee security.
Source Defense neutralizes these threats by often being the first to blacklist malicious domains based on the latest research findings, blocking or isolating risky scripts, monitoring behavioral patterns—including first-party—and detecting malicious actions in real time.
