ONGOING MAGECART VARIANT HIDES MALICIOUS CODE IN BROKEN IMAGE TAGS
July 1, 2025
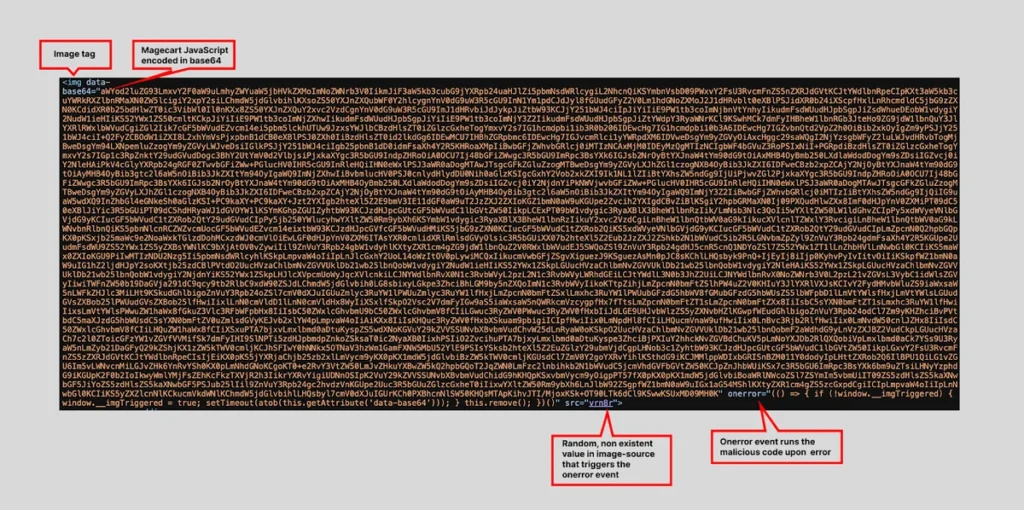
Our research team at Source Defense has uncovered a stealthy Magecart-style attack targeting dozens of e-commerce websites worldwide across various industries. This novel technique hides malicious JavaScript inside a Base64-encoded payload embedded in an image tag — making detection and mitigation significantly more challenging. Furthermore, this attack operates within the first-party context, which makes it invisible to most client-side security tools.
How the attack works
Unlike traditional Magecart campaigns that inject external scripts or use third-party services (like compromised GTM containers), this variant leverages a malformed <img> tag with the following features:
- src=”wag2e”: A broken image source to trigger the onerror event.
- data-base64: A Base64-encoded payload containing the malicious code.
- onerror: When the image fails to load, this event decodes and executes the Base64 script.
Once executed, the payload:
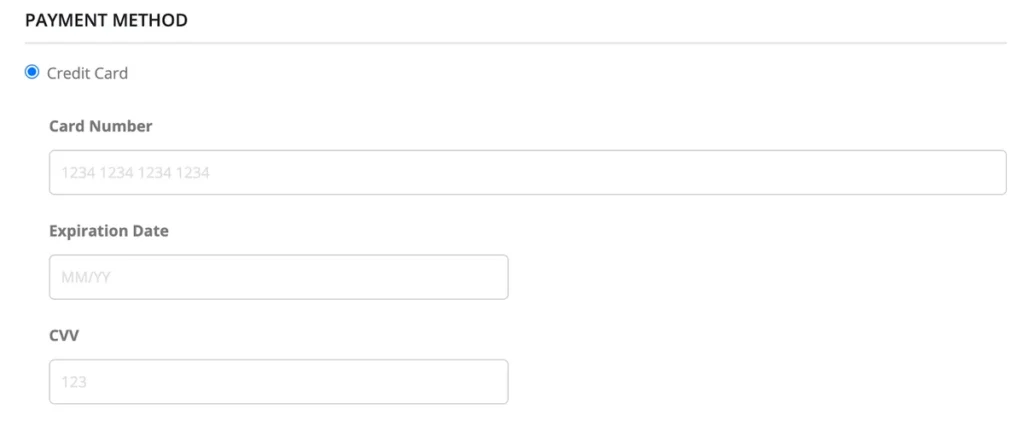
- Uses a “double-entry” magecart method to replace the legitimate payment form with a fake clone (see image below).
- Captures payment details, including credit card number, expiration, and CVV.
- Sends the stolen data to a network of malicious domains controlled by the attacker.
How does Source Defense Keeps You Safe
Source Defense can detect and report data exfiltration attempts, even when running from first party scripts.
For this attack, the following alerts will be triggered:
- Outbound data is sent to blacklisted malicious domains.
- In the same session, PCI data is being accessed.
As part of our ongoing research, all identified domains used by the attacker have been added to the Source Defense blacklist.
Key takaways
- Attackers are increasingly sophisticated, embedding malicious logic in unconventional locations.
- This variant bypasses most CSPs and security controls due to its execution from a 1st-party context.
- Visibility into client-side behavior is essential — and Source Defense remains committed to tracking, analyzing, and blacklisting these threats in real-time.