MAGENTO FEATURE ABUSED TO BYPASS PAYMENT PROVIDER AND STEAL CREDIT CARDS
Attackers have discovered a clever new way to steal credit card data: by turning one of Magento’s own features against it. They hijacked a trusted part of the eCommerce platform that’s used to refresh customer-specific content – like the shopper’s name, cart summary, and shipping details – during checkout without reloading the page.
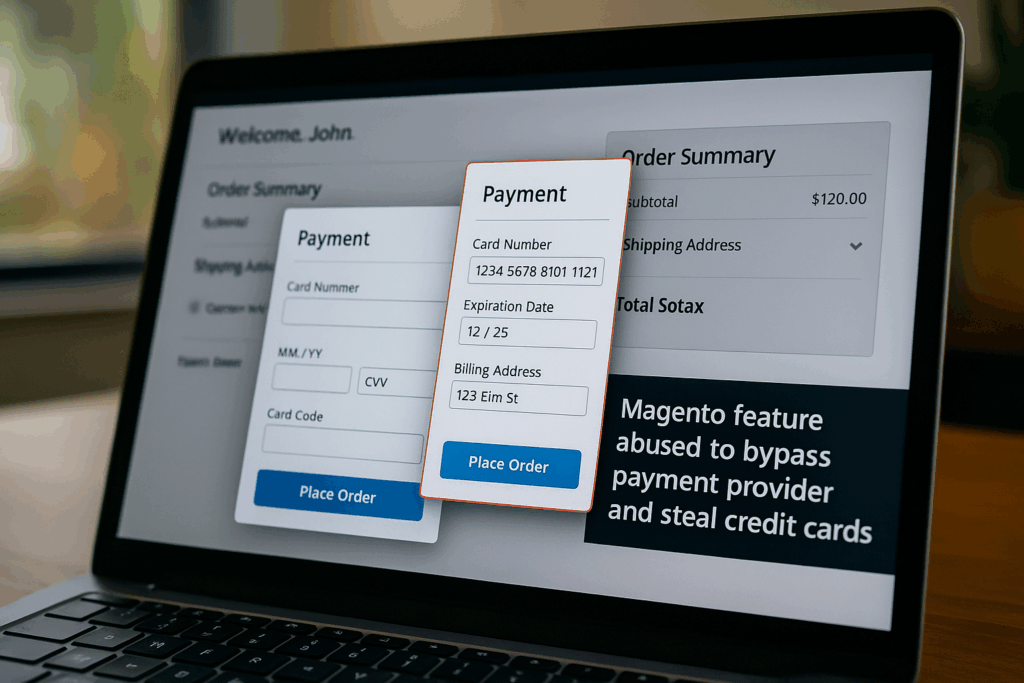
Instead of displaying a simple shipping message, the compromised site secretly delivered malicious code that injected a fake payment form before the real payment service provider (PSP) flow appeared, quietly capturing customer and payment information in a classic “double-entry” attack.
This technique undermines the perceived safety of using a PSP and can give organizations a false sense of security.
To make matters worse, everything happened inside the site’s own code and domain, with no additional network calls to load scripts or send data – the stolen details were sent only back to the same site – so most traditional security tools would have nothing unusual to flag.
Attack details
In this case, the attackers took advantage of Magento’s background “customer sections” feature, a mechanism the platform uses to quietly update data like who is logged in, what’s in the mini-cart, and what shipping policies to show. One of those sections, which should have contained nothing more than a simple shipping policy message, was abused to deliver hidden JavaScript instead. The text field was quietly swapped for a script block that held heavily scrambled code, delivered directly from the compromised server with no need for additional third-party script loads.
When a shopper reached the checkout page, that code was decoded in the browser and turned into a live script. It injected a fake payment form that closely resembled the legitimate PSP experience and encouraged the shopper to enter card details, creating a seamless flow that felt normal. As soon as the customer filled out the fake form and clicked to continue, the script collected the personal and payment data – including card number, expiry date, and billing address – and sent it only to the same site, so no separate, suspicious request to a new domain was needed. From the outside, the network traffic looked like a normal transaction with a trusted payment provider, allowing the attack to blend in and bypass many traditional controls.
How Source Defense protects you
Source Defense monitors and governs the behavior of all scripts in real-time, including first-party ones like this. Even though the attack originates from Magento’s own system and targets a checkout that appears to be safely handled by a PSP, Source Defense would detect and report several suspicious behaviors, including Accessing PCI data and Executing risky actions.
By continuously monitoring all client-side scripts on payment pages, including first-party logic that wraps or mimics payment provider flows, Source Defense gives security and compliance teams the visibility they need to quickly spot and investigate potential breaches. This remains true even when both the malicious script and the captured data stay on the trusted first-party domain.
How you’d be alerted
If such a threat would be active on your website, Source Defense would issue the following clear, high-signal alerts rather than raw log noise.
New Behaviors Identified:
- Accessing PCI data
- Accessing PII data
- Executing risky actions
These alerts are prominently displayed in the bell notification center, the dashboard summary and on the script’s page new behaviors. Email and webhook event are triggered to those who opt in to the respective channel.
Summary
This was an unusual attack: a server-side compromise that led directly to a stealthy, hard-to-find client-side exploit. It didn’t rely on sketchy domains or obvious third-party code, but instead abused trusted Magento infrastructure to inject and execute malicious JavaScript from within a legitimate feature, then layered a fake payment form on top of a seemingly safe PSP checkout to trick users into a double entry of their card details.
Most security tools wouldn’t see this coming because it happens “inside the walls” of the site, hidden in normal application behavior and without additional network calls that would stand out from typical PSP traffic.
Source Defense provides a critical last line of defense by actively monitoring and controlling what scripts are allowed to access and transmit at runtime, a capability that has become essential for detecting and stopping advanced, hybrid attacks like this – even on PSP-backed checkout flows – before they turn into full-blown breaches.