MAGECART RETURNS: THREAT ACTORS REBRAND GTM-HIDING ATTACKS
June 3, 2025
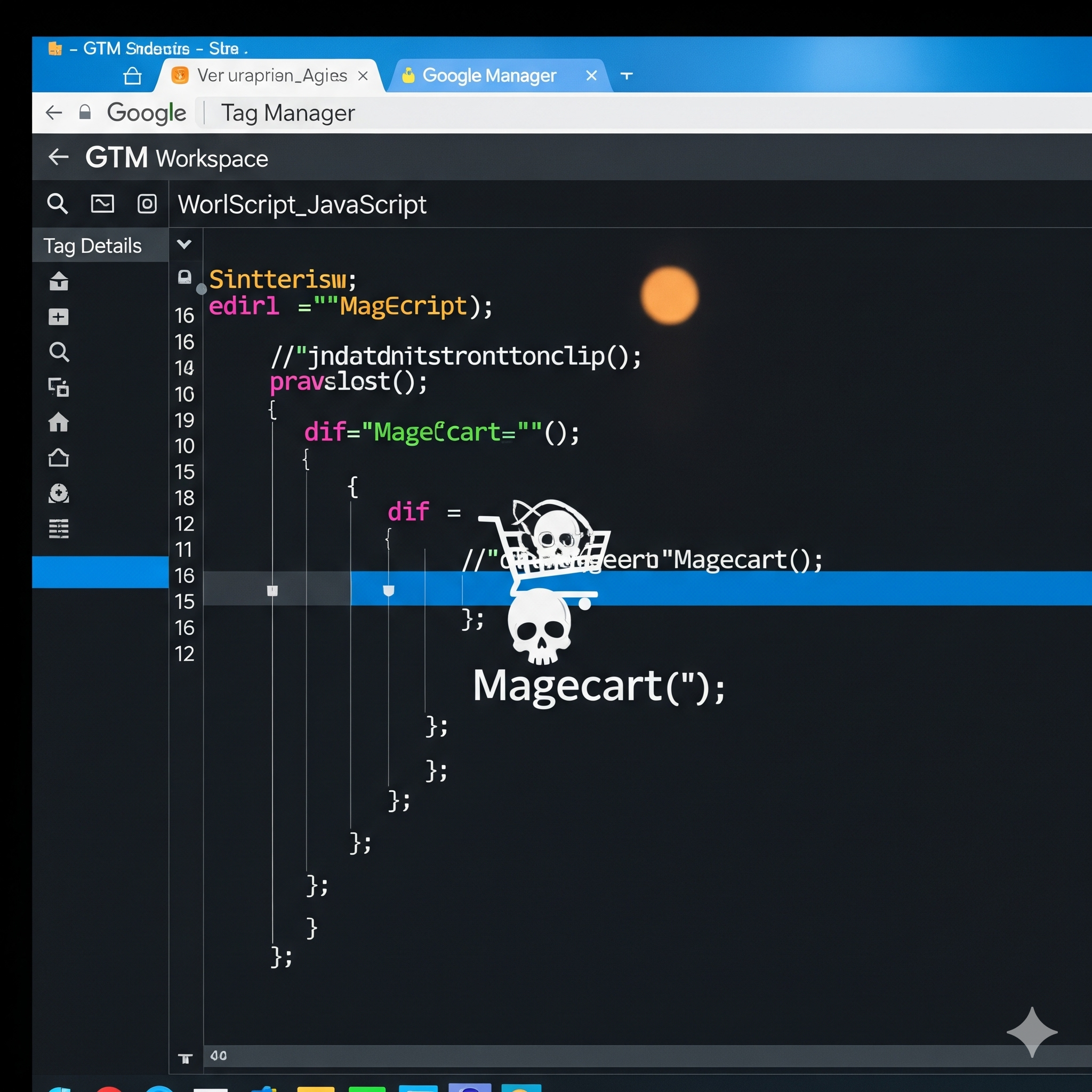
The Source Defense Research Team has observed an infrastructure shift in a persistent Magecart campaign. The attackers have reactivated a previously dormant domain—jqueri[.]at—continuing their established strategy of hiding malicious scripts behind Google Tag Manager (GTM) containers. This move is part of an ongoing effort to stay ahead of domain blacklists and maintain a foothold across targeted websites.
Attack summary
Over the past year, our team has tracked the use of GTM containers to inject innocent-looking scripts tied to the following domains served from the same IP address:
- jsdelivr[.]at – observed in 13 GTM IDs.
- gstatis[.]co – observed in 18 GTM IDs.
Although jqueri[.]at had remained inactive during that time, in May 2025 we detected a shift:
- gstatis[.]co stopped serving malicious payloads.
- 17 GTM containers previously linked to gstatis[.]co began loading jqueri[.]at, also from the same IP address.
- A new GTM ID and a direct reference to jqueri[.]at were found on a compromised merchant’s site
This evidence points to an intentional rebranding by the attackers—designed to circumvent static domain blocks while continuing to operate via GTM infrastructure.
Key Takeaways
- GTM remains the core delivery mechanism: Scripts injected via GTM are hard to detect, as they are injected dynamically and don’t require modification of a site’s source code.
- Domain swapping maintains stealth: Replacing gstatis[.]co with jqueri[.]at helps evade blacklists.
- Familiar infrastructure, new domain: The shift shows the group’s continued reliance on GTM, highlighting its value in enabling persistence and obfuscation.
- Script names deliberately resemble valid known-services to evade detection.
How does Source Defense protect you
Intelligence-driven threat detection: Continuous monitoring of GTM behavior and domain reassignments allows us to quickly identify and block threats.
Real-time protection with Protect: Customers using this product receive automated blocking for scripts tied to known malicious GTMs or domains.
Proactive alerts with Detect: Customers are notified when:
- Scripts attempt to access PCI/PII
- Malicious domains like jqueri[.]at are contacted
As attackers adapt their tactics, staying ahead requires real-time visibility, rapid response, and deep understanding of client-side threats—exactly what Source Defense delivers.