MAGECART ATTACK VIA 1X1 SVG & WEBSOCKETS
August 12, 2025
The Source Defense Research Team has uncovered a new Magecart campaign impacting over 50 e-commerce websites, most located in Europe. This highly evasive attack uses an unusual loader — a fake 1×1 pixel SVG (Scalable Vector Graphics) file — to bypass traditional detection methods and deliver its malicious skimming payload via a WebSocket connection.
SVG (Scalable Vector Graphics) is a common web image format used to display graphics such as icons, charts, and logos. It’s XML-based, lightweight, and can scale to any size without losing quality. SVG files can also include embedded scripts for interactive features — and it’s exactly this feature that attackers are exploiting here to conceal and run malicious JavaScript code.
Attack overview
Once the SVG is loaded, an obfuscated first-party JavaScript embedded in the onload attribute executes. This script opens a WebSocket to one of several attacker-controlled domains, including:
elementatorprof[.]info
ghanamusthi[.]xyz
asd123qwe2[.]online
wsocket[.]store
jquerystatic[.]com
cloudflare-stat[.]net
orristhekyone[.]site
api-chat[.]live
jscode[.]cloud
googlestgmanager[.]xyz
jquerytestingus[.]com
jquerymanagerus[.]com
The Magecart script itself is not present in the page source — instead, it is delivered as an incoming WebSocket message.
Attack techniques
Two primary skimming methods were observed in this campaign:
Silent Skimming – Capturing payment details entered into legitimate checkout forms, sending them directly to attacker infrastructure without altering the user experience.
Double-Entry Attack – Injecting a highly convincing fake payment form, complete with site-specific branding, then passing users back to the real payment process after harvesting their data.
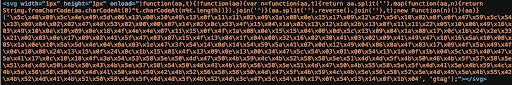
The obfuscation uses string reversal and XOR-based decoding to conceal the malicious JavaScript. Below is an excerpt from an actual infected SVG tag:
How Source Defense protects you
Behavioral Analysis: Even if a WebSocket is opened to a previously unknown domain, Source Defense flags and blocks suspicious behaviors such as Accessing PCI/PII data and Sending data to blacklisted or unrecognized domains.
First-Party Script Monitoring: Our platform inspects both third- and first-party scripts, detecting unusual loading methods.
Automatic Policy Blocking: For Protect customers, any identified malicious domains are immediately blocked. Detect customers receive alerts for manual intervention.
How You’ll Be Alerted
If this attack were active on your site, you would receive alerts for:
New First-Party Script Behaviors Identified – Flags unknown or suspicious scripts.
New Behaviors Identified:
- Accessing PCI data
- Accessing PII data
- Sending data to blacklisted domain
These alerts will be visible in:
- Bell Notification Center
- Dashboard Summary (marked in red)
- ‘Found in Blacklists’ & ‘Script Behaviors’ widgets (highlighted in red)
Key takaways
- SVG files, while legitimate and useful for web graphics, can be weaponized to execute hidden malicious scripts.
- The attack blends first-party script compromise, WebSocket payload delivery, and obfuscation to avoid static and domain-based detection.
- Over 50 European e-commerce sites were affected — highlighting the need for global vigilance.
- Comprehensive client-side monitoring that includes first-party assets and unconventional file types is critical to defense.
