In late January, Malwarebytes reported that Segway, the manufacturer of insanely cool (*editors opinion), self-balancing, single-rider vehicles, was the victim of a Magecart attack. The attack may have exposed up to 600,000 visitors to malicious code embedded within Segway’s webpages. When customers entered payment details into the Segway website that information was exposed to hackers as well, potentially leading to credit card fraud, identity theft, and damage to Segway’s revenue and reputation.
This isn’t a “victim shaming” post – to the contrary, in December of 2021, Source Defense penned an article in SC Magazine predicting and warning that Magecart attackers would be on the move during the holiday season (and beyond) given the meteoric rise in e-commerce/online transactions over the past two years. Our opinion is that Segway is likely just the tip of the iceberg in terms of organizations recently impacted.
We said then – believe firmly – and are supported by this and other recent disclosures, that client-side attacks represent a real and material 3rd party risk to any organization that collects sensitive information on its web properties.
From Clever Hack to Endemic Risk
Magecart is a term coined by the security community to describe a number of attack groups who all employ similar techniques and tools. Magecart Group 12 is the specific group identified in this attack. That group alone is responsible for compromising tens of thousands, if not hundreds of thousands, of websites all using the same techniques.
The word “Magecart” itself is a combination of two words, “Magento” and “shopping cart,” which describes the origin of the very first instances of this type of attack – the shopping cart module within the Magento web ecommerce platform.
Over seven years have passed since the first Magecart attack was observed, and as time has passed, attacks have grown in both sophistication and impact. Today, a “Magecart” attack can mean any attack perpetrated within the webpage that a company provides to their visitors, whether that company utilizes Magento or not, or even if that company is completely uninvolved in online commerce.
Banks, financial services companies, healthcare organizations, and event governments have been victimized in this same fashion. Because of this evolution, Source Defense and others in the cybersecurity community have begun to refer to these incidents as “client-side attacks,” meaning that they are attacks which occur within a website visitor’s web browser, rather than within a company’s own infrastructure. Just recently, Gartner coined the phrase “web application client-side protection” to define the category of solutions dealing with client-side attacks, and predicted that mass market adoption of these solutions is just a few short years away.
Everything Old Is New Again
The Segway breach is an interesting example of both old and new techniques. Segway was indeed using Magento – the platform is still widely used today – which allowed Group 12 a way into the company’s web application. Once attackers had access, they leveraged a newer technique by hijacking the behavior of something called a “favicon” file.
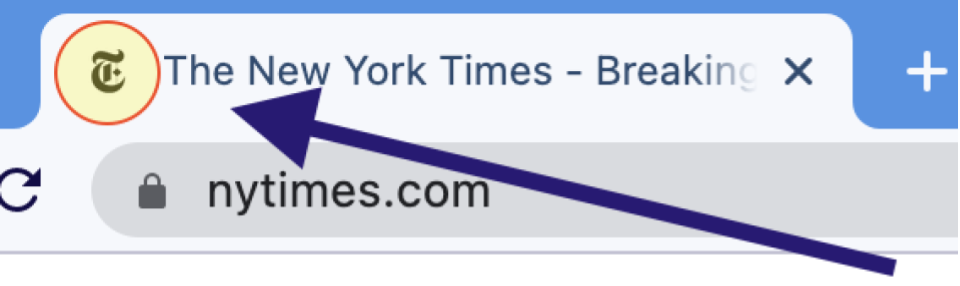
A “favicon” file is a type of file used by websites to tell web browsers what icon should be presented next to their URL inside the browser’s interface.
Attackers were able to inject their own malicious code into the faviconimage itself, thereby hiding the payload from website scanning and code analysis tools. Once the favicon image was retrieved by the web browser, the code was executed and the attack could unfold within the webpage itself.
Because web browsers allow any code running inside the browser to have complete access to any information present on the web page, attackers were then able to “skim” payment information directly from the visitor’s browser. Once collected, attackers can send the information anywhere they like simply by leveraging the browser’s own native abilities to open network connections to other computers on the Internet.
The Segway attack illustrates two important takeaways about client-side attacks:
They are a persistent and established risk to every website, irrespective of platform, technology, or purpose
They continue to evolve in new and creative ways to thwart traditional cybersecurity technologies and methodologies
Learning from the Past, Controlling the Future
Source Defense believes that the best approach to defeating client-side attacks and eliminating client-side risk is by taking a proactive approach and utilizing technologies which can stop the attacks before they inflict damage on your business or your visitors. By managing the code running in your web pages, within your visitors’ web browsers, the Source Defense client-side security platform enables real-time control over what client-side code can and cannot do, stopping even novel and inventive attacks before they can do harm.
The Source Defense client-side security platform was designed from the ground up to provide not only ironclad security but also burden-free deployment and on-going use. Source Defense deploys with just two lines of code, or is easily added via a suite of off-the-shelf integrations. On-going upkeep and monitoring is usually only a few hours per month, ensuring that solving a new problem doesn’t stress already over-taxed security teams.
If you are interested in learning more about Source Defense, feel free to request a risk report for your own website, book a personal demonstration, or join us at one of our upcoming events.
