by Source Defense
Stolen Data at the Point of Input: Real Attacks on Patient Portals
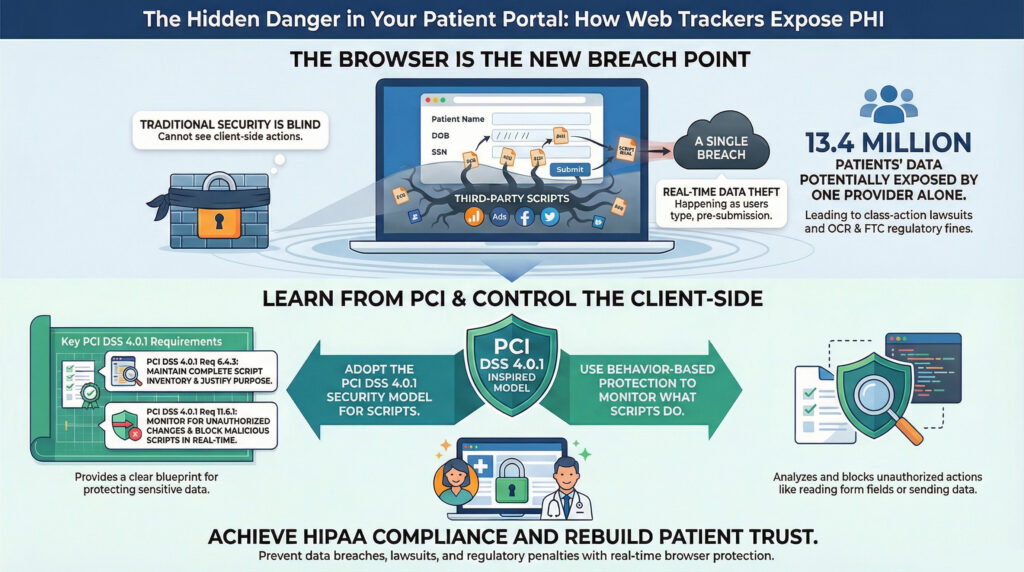
In early 2024, Kaiser Permanente revealed that third-party tracking scripts on its websites and mobile apps had potentially exposed the personal data of 13.4 million patients. Around the same time, hospitals like Goshen Health and Hancock Health faced class-action lawsuits for using web trackers such as Meta Pixel that allegedly sent patients’ protected health information (PHI) to Facebook without consent. In yet another case, a healthcare system found its use of Google Analytics had shared PHI with an advertising platform for nearly three years.
These incidents have something in common: the theft or exposure of sensitive data happened in the browser as users typed into a form, not from a hacked database or breached server. In every case, the threat came from third-party JavaScript embedded in the healthcare provider’s website. This is the new reality: cybercriminals (and even misconfigured trackers) are exfiltrating data at the point of input, in real time, using the patient’s browser as the attack surface.
How Web Trackers and Third-Party Scripts Leak PHI
Healthcare websites often rely on dozens of third-party scripts: for analytics, chat tools, advertising pixels, maps, and appointment scheduling widgets. Every one of those scripts has access to what’s happening in the browser. If any script is compromised or behaves beyond its intended use it can quietly collect sensitive data from web forms, including login credentials, health information, or contact details.
This is how “formjacking” or “digital skimming” works. A compromised script records what a user types into a form, often sending the data to a third party in real time. The worst part? This typically goes undetected by traditional security tools because it never touches the server. The data is siphoned out before the patient even hits submit.
Even when scripts aren’t compromised, they can still violate privacy. Many tracking tools collect more than they should, sharing identifiers and page context with marketing platforms. If a tracker on your portal shares a patient’s page visit or symptom search with Facebook or Google, it could constitute an unauthorized disclosure under HIPAA.
Why Traditional Defenses Fall Short
Most healthcare organizations have hardened their server-side security. Firewalls, encryption, vulnerability scanning, endpoint protection. All of it helps. But none of it sees what third-party JavaScript is doing in the browser.
Content Security Policies (CSP) and Subresource Integrity (SRI) are supposed to help. In theory, CSP restricts where scripts can be loaded from, and SRI ensures that scripts haven’t been altered. But in practice, CSP is difficult to manage and often overly permissive to avoid breaking functionality. SRI doesn’t work well with scripts that change frequently (which most third-party scripts do). Neither gives you real-time insight into what scripts actually do once they’re running.
Put plainly: CSP and SRI may provide a false sense of control. They don’t stop scripts from leaking PHI. They don’t alert you when behavior changes. And they can’t tell you which scripts are accessing which fields or sending data offsite.
The Regulatory and Legal Risks
HIPAA requires covered entities to safeguard protected health information regardless of whether that data is stored, transmitted, or in use. That includes information entered into a form before it’s submitted. The Office for Civil Rights (OCR) has made it clear that using third-party tracking technologies on healthcare websites can lead to impermissible disclosures of PHI.
And the consequences are serious. Healthcare providers have faced multi-million dollar class action lawsuits for using web trackers without adequate safeguards. Others have been hit with enforcement actions from the Federal Trade Commission (FTC) for deceptive data sharing. These are not theoretical risks, they are active investigations, lawsuits, and settlements playing out across the industry.
If your patient portal is silently leaking data to advertisers or compromised vendors, it’s not just a privacy violation, it’s a regulatory failure.
A Model Worth Borrowing: PCI DSS 4.0.1 and Client-Side Security
While HIPAA mandates that healthcare organizations protect PHI, it stops short of specifying how to secure the browser layer. The payment card industry, on the other hand, has moved decisively. As of March 2025, PCI DSS 4.0.1 introduces two requirements, 6.4.3 and 11.6.1, that directly address client-side script risk.
Requirement 6.4.3 mandates that organizations:
- Maintain a complete inventory of all scripts on payment pages
- Justify the presence and purpose of each script
- Confirm the integrity and authorization of each script
Requirement 11.6.1 takes it a step further:
- Monitor payment pages for unauthorized changes at least once every 7 days
- Detect and block malicious scripts in real time
Together, these requirements close the gap that client-side threats exploit. They recognize that it’s not enough to protect the server, you must control what executes in the user’s browser.
Why Healthcare Should Pay Attention
If your organization handles payment card data, PCI DSS 4.0.1 already applies. But even if you’re not directly processing payments online, these requirements represent a best-practice model for securing client-side environments. The parallels to HIPAA are clear:
- PCI focuses on cardholder data; HIPAA focuses on PHI.
- Both require protection against unauthorized access or disclosure.
- Both hold organizations accountable for risks introduced by third parties.
In short, PCI DSS 4.0.1 requirements offer a blueprint for what HIPAA-aligned client-side controls should look like.
HIPAA Compliance, PCI Alignment, and Patient Trust
At a time when OCR is warning about web tracker violations, FTC is pursuing enforcement, and patients are suing over PHI leaks, taking control of your client-side security is more than proactive-it’s essential.
Behavior-based runtime protection:
- Helps prevent impermissible disclosures under HIPAA
- Aligns with PCI DSS 4.0.1’s real-world requirements for script control
- Reduces the risk of lawsuits, breaches, and reputational damage
You don’t have to guess what’s running in your patients’ browsers anymore. You can see it. Control it. Prove it.
Behavior-Based Protection: A Practical Path Forward
What healthcare organizations need is real-time visibility, dynamic enforcement, and low operational overhead. That’s where behavior-based client-side protection comes in.
Solutions like Source Defense:
- Inventory all scripts, including nested third- and fourth-party code
- Analyze script behavior in real time – not just where they came from, but what they do
- Block unauthorized behaviors, such as reading keystrokes, accessing form fields, or transmitting PHI
- Alert your team to policy violations and suspicious changes
Instead of relying on a whitelist of domains or fragile hash values, behavior-based platforms enforce policy by observing what scripts try to do. If a new script attempts to capture patient data or modify page content unexpectedly, it’s flagged or blocked immediately.
This approach doesn’t just improve security. It supports compliance. By continuously monitoring and controlling scripts at runtime, organizations can demonstrate safeguards aligned with HIPAA’s technical standards and with PCI DSS 4.0.1’s script control mandates.
Traditional security tools weren’t built to see inside the browser. Behavior-based solutions were designed for it. With Source Defense, healthcare organizations can:
- Deploy protection with two lines of code
- Get up and running in days, not months
- Offload ongoing monitoring and script evaluation to an automated engine
- Integrate policy recommendations and alerts directly into security workflows
Source Defense has been independently reviewed by leading PCI QSA firms like CoalFire and VikingCloud. It’s trusted by over 1,000 brands, including major healthcare systems, and helps prevent billions of potential security and privacy violations each year.
Take Control of Your Patient Portal’s Client-Side Risk
Get the tools to lock down your digital supply chain and protect sensitive data at the point of input.
Download the “Web Client Runtime Security in Healthcare” eBook or Request a Demo to get started today.
